Your comments
Hey Josh,
I’ve heard back from the host. They can’t provide a specific rule ID or line reference from the malware engine.
However, they’ve confirmed this is a pattern-based detection and have offered to submit the flagged file to their malware provider for manual analysis and signature whitelisting if it’s deemed safe.
From my side, the likely triggers still appear to be the use of remote file_get_contents() calls, third-party proxy endpoints, direct file deletion via unlink(), and legacy input handling patterns.
I’ll proceed with the host’s malware analysis submission, but longer-term it would be good to refactor these areas to avoid repeat false positives across other hosts and security tools.
I’ll update you once the malware provider responds.
Regards,
Aaron
Hi Josh,
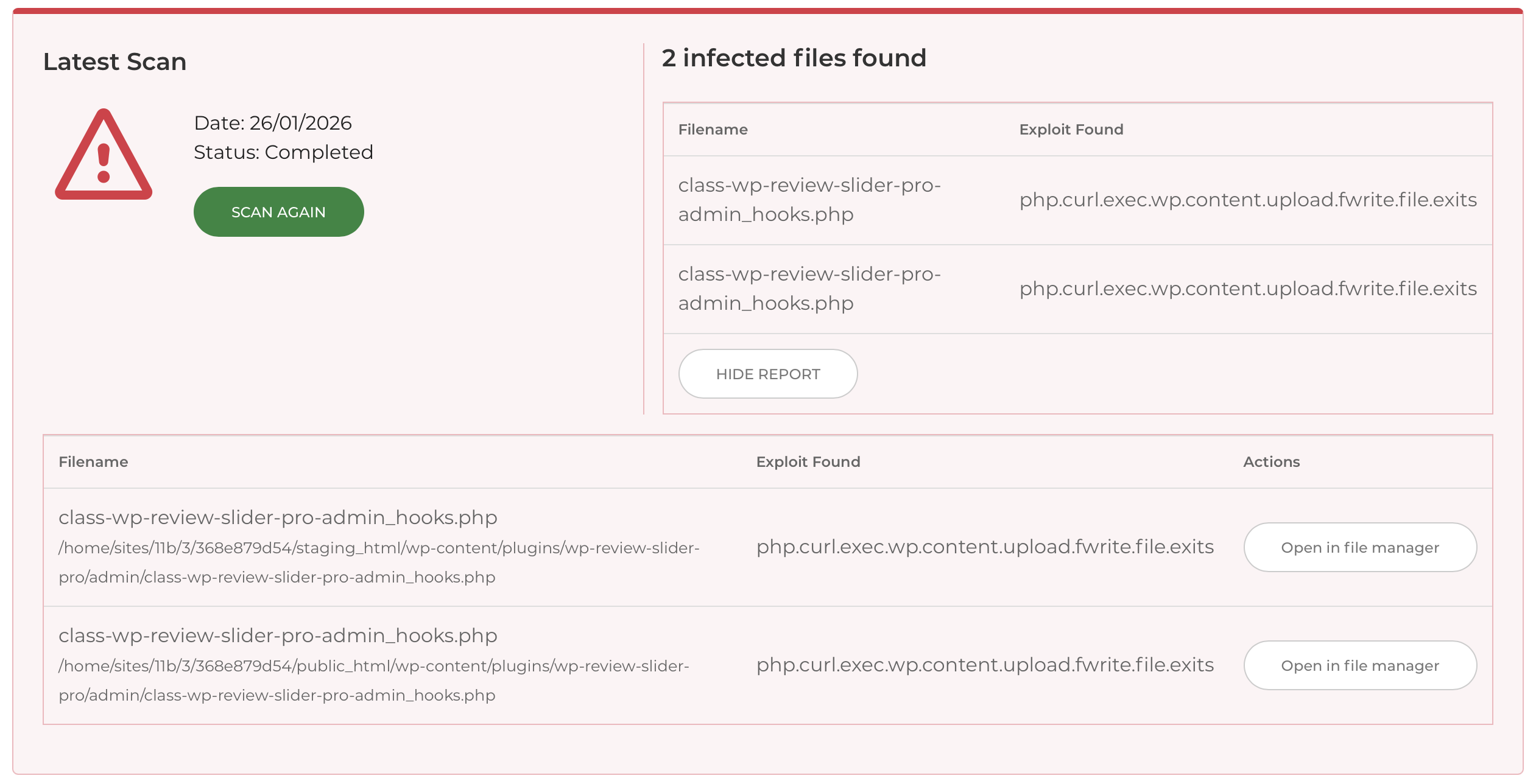
This is being scanned using the malware checker through the hosting provider 20i. It's giving a report that reads the following:
| class-wp-review-slider-pro-admin_hooks.php /home/sites/11b/3/368e879d54/public_html/wp-content/plugins/wp-review-slider-pro/admin/class-wp-review-slider-pro-admin_hooks.php | php.curl.exec.wp.content.upload.fwrite.file.exits" |
I hope that helps
Customer support service by UserEcho


Hi Josh,
I have heard back from our hosting provider and they have heard back from their "malware expert" who has now whitelisted the file. I have re-run the malware scanner and I'm pleased to say that there is no issues found now it's been whitelisted.
Many thanks for your prompt and professional approach to this.
Kind Regards,
Aaron